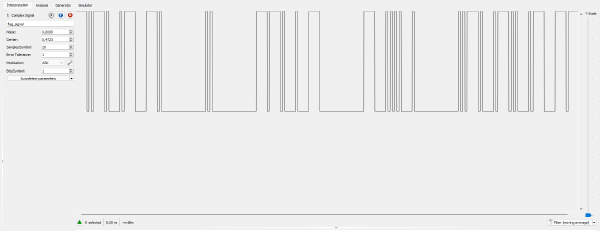
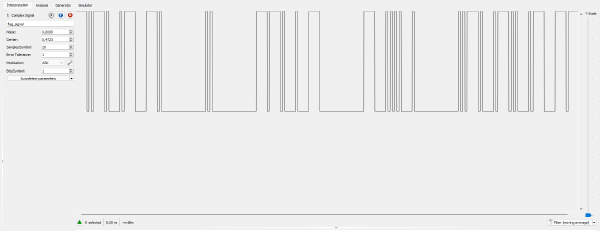
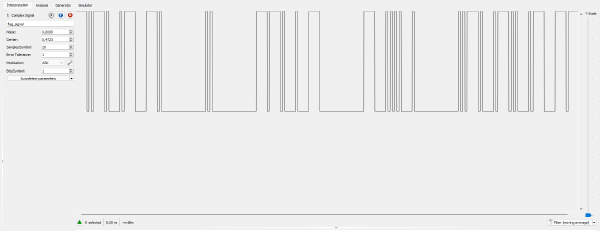
IQ signal crafting to communicate with a morse telegraph server
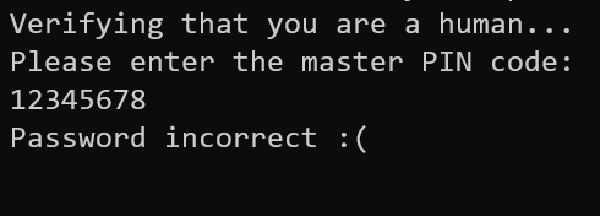
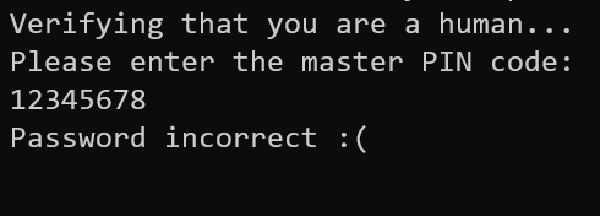
Recovery of a PIN code using a timing based side channel attack
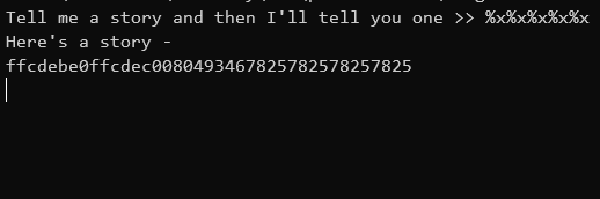
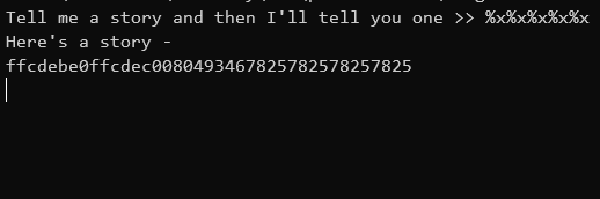
Format string exploitation to leak a variable on the stack
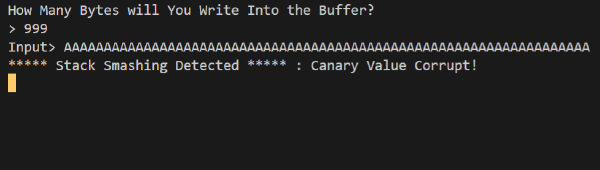
Corrupted magic bytes recovery
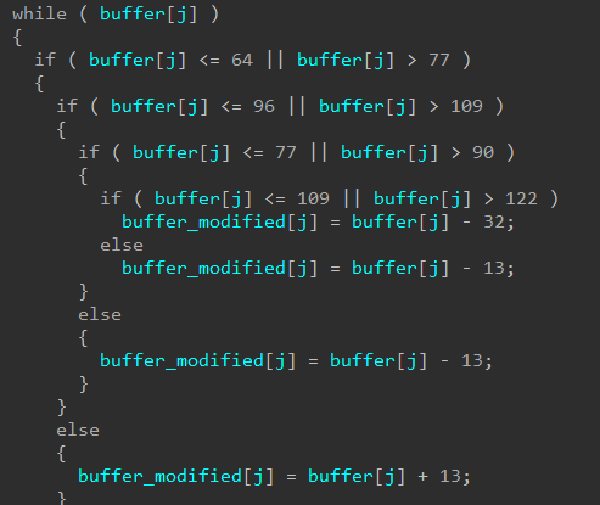
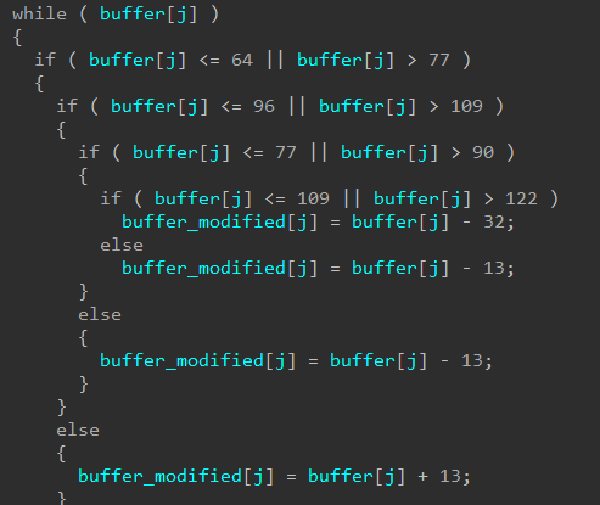
Basic reverse of comparative algorithm
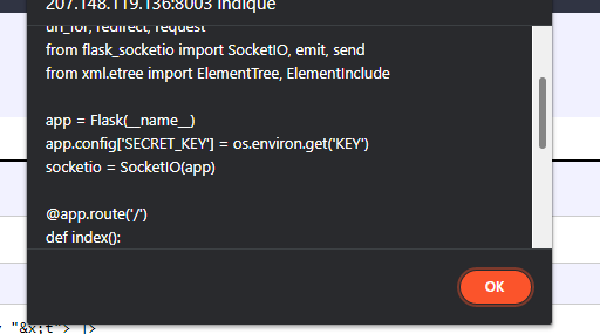
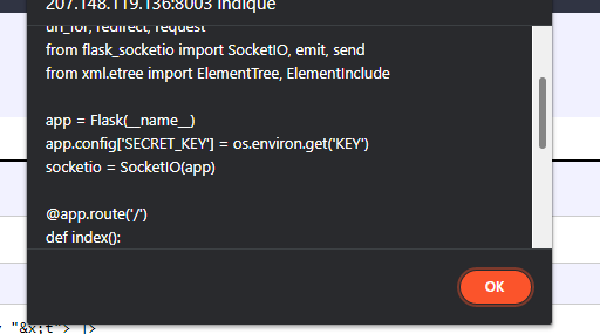
XInclude abuse and filter escape to read local files
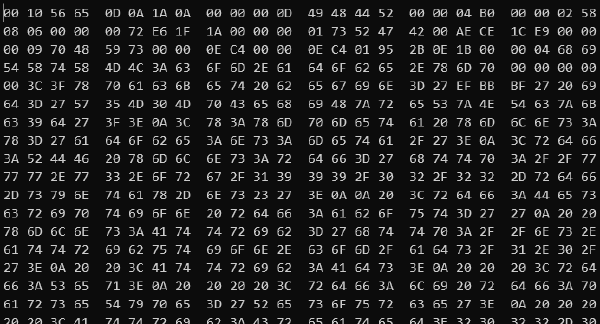
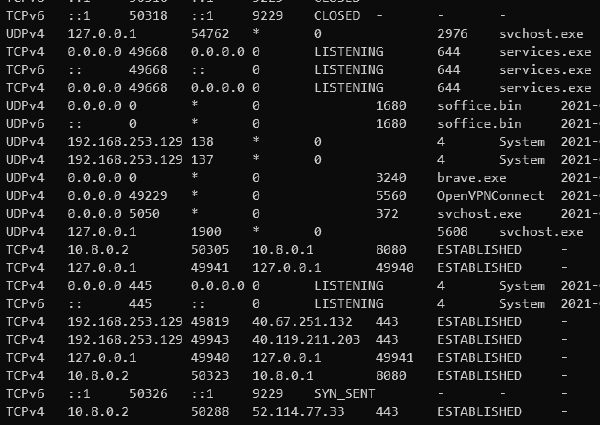
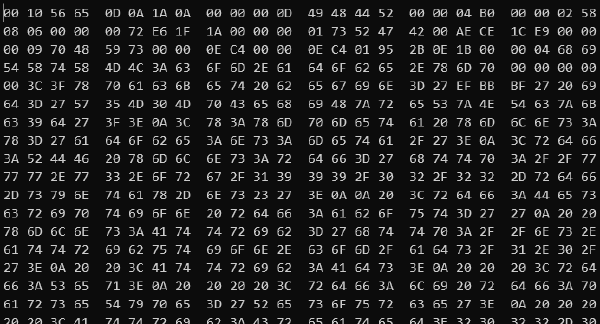
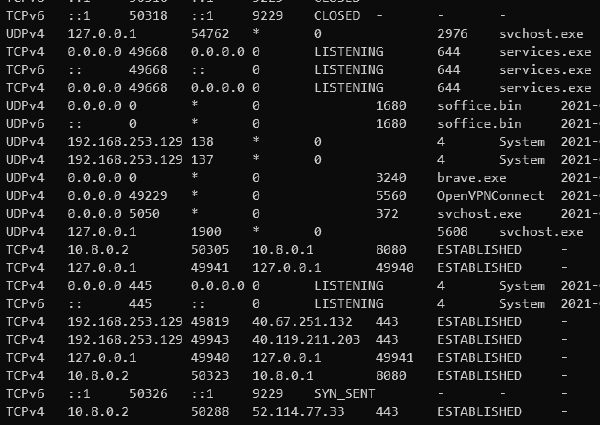
A memory dump analysis to retrieve an established connection IP and port
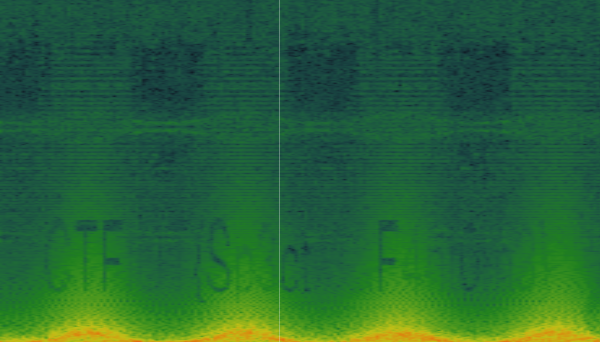
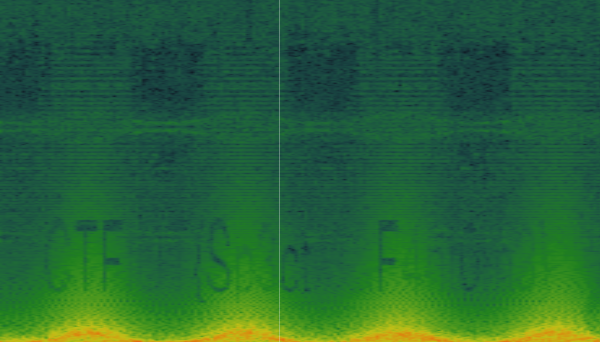
Recovery of the flag from the spectrogram of a mp3 file
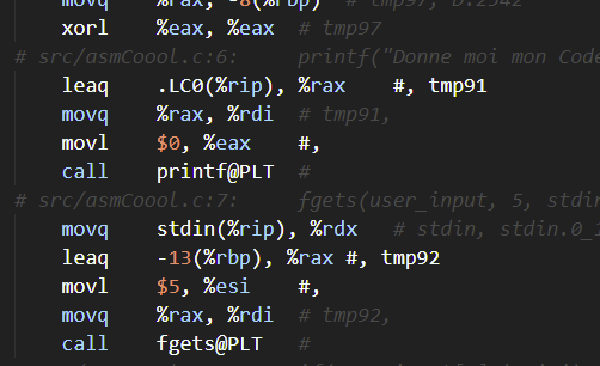
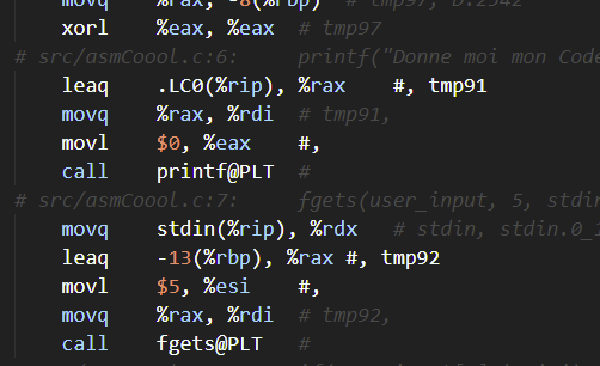
Hand written assembly program analysis