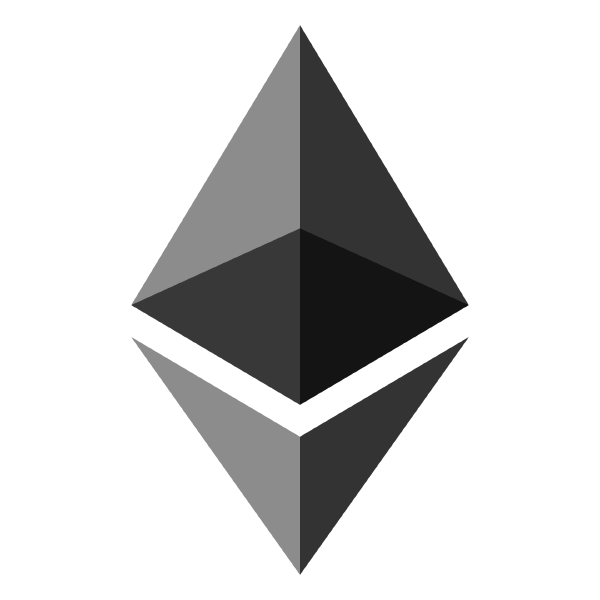
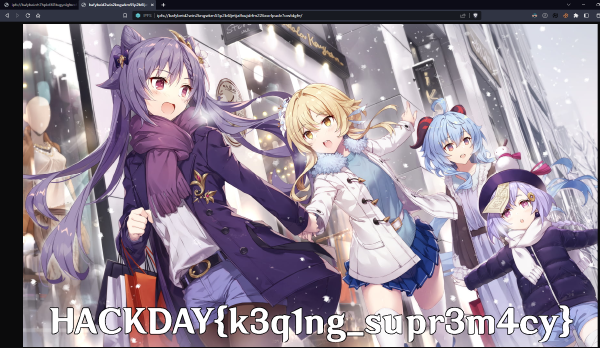
Serial code verification based on equations
Privileges check bypass and storage slot computation
Recovery of deployed contract address and inspection of NFTs metadata on IPFS
Exploitation of tx.origin and delegatecall to steal ERC20 tokens
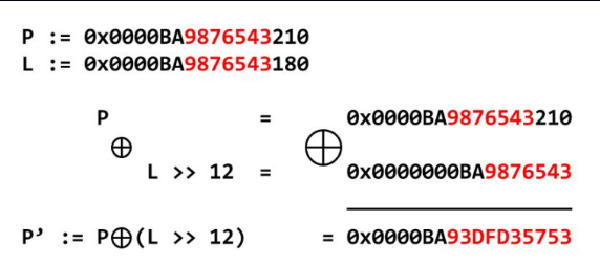
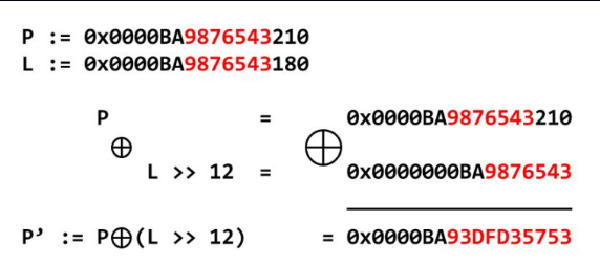
tcache poisonning with safe linking
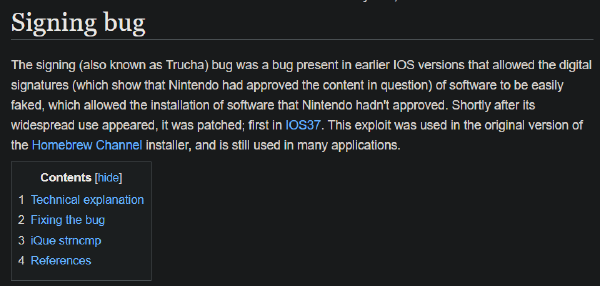
RSA signature bypass due to vulnerable implementation
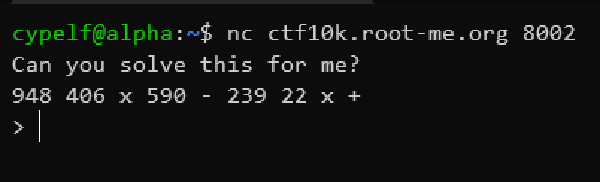
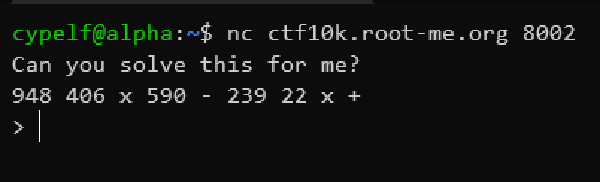
Reverse polish notation expressions computation
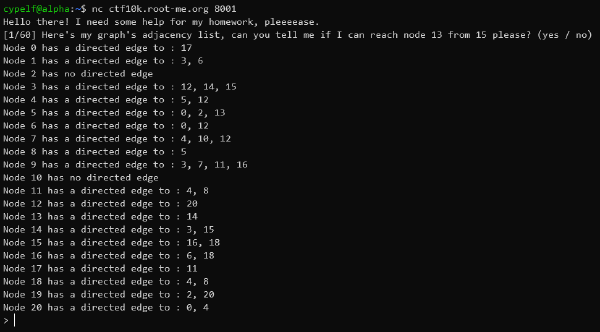
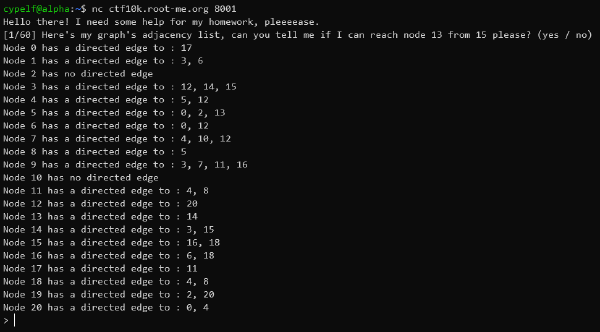
Depth first search algorithm application on an oriented graph
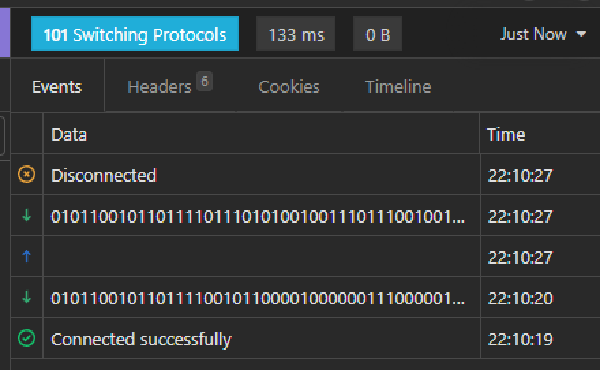
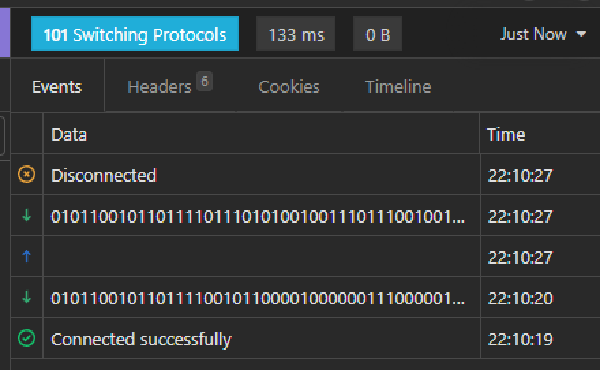
Websocket based physics quizz automation
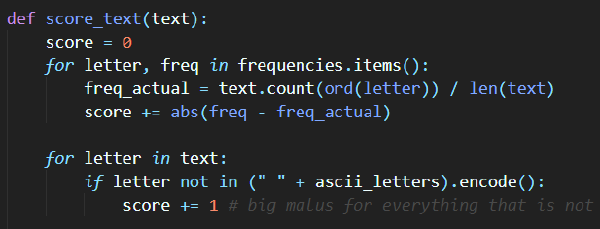
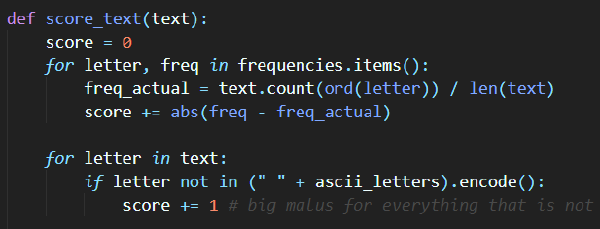
Hamming distances computation and frequency analysis to recover an unknown XOR encoded message