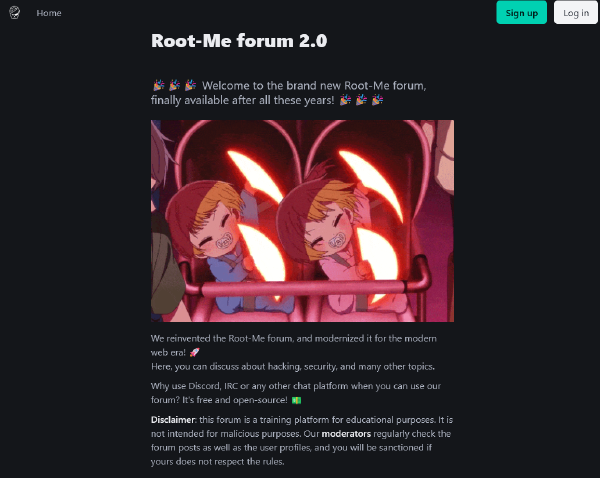
Jinja filter bypass to XSS
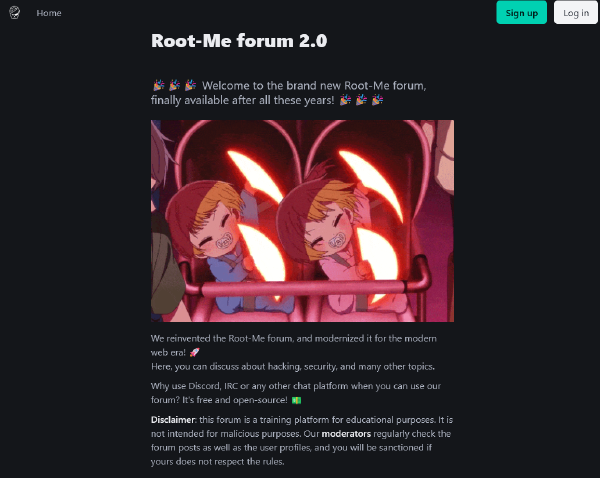
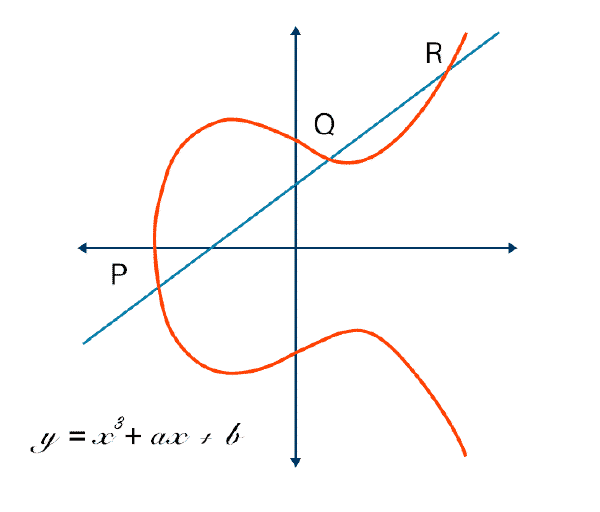
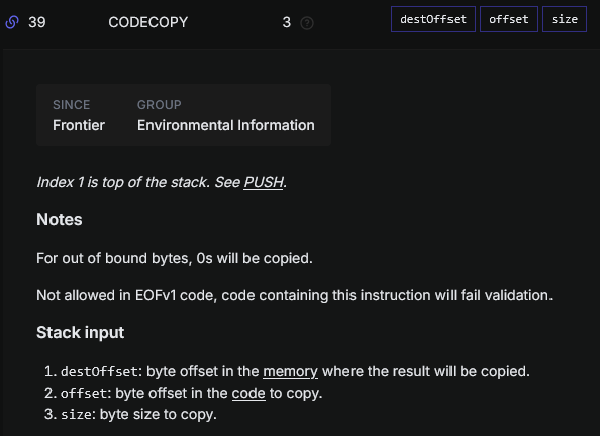
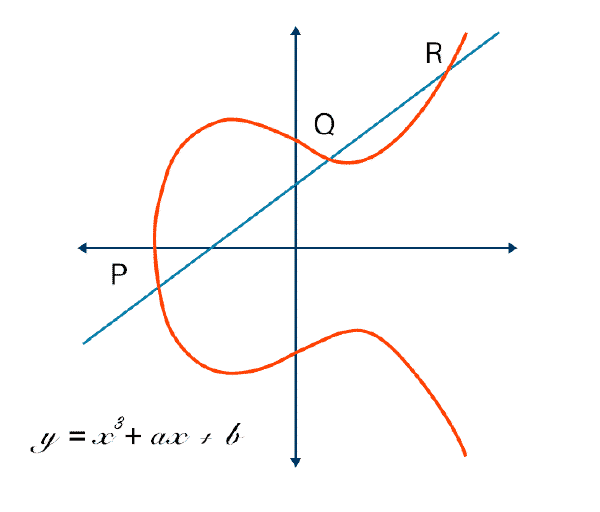
Writing EVM opcodes manually and abusing CREATE2
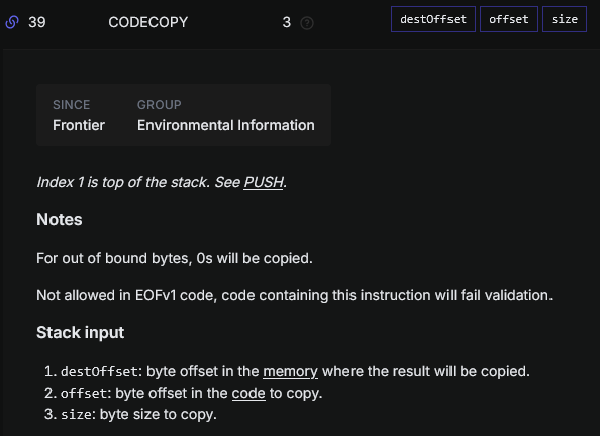
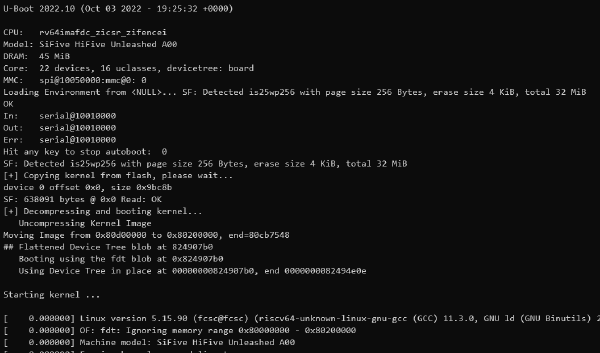
Dump of a remote Linux kernel through u-boot shell
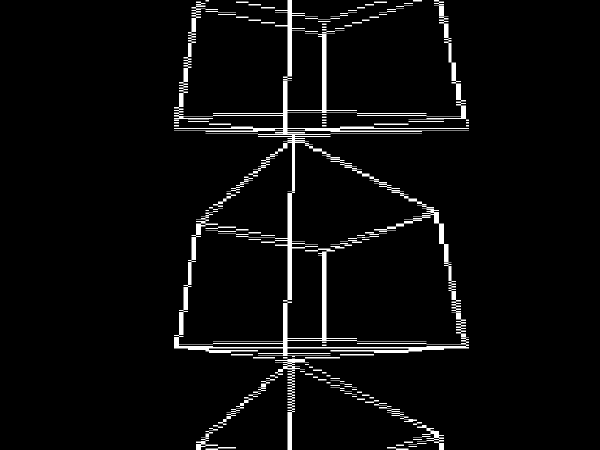
Extract the video of a digitized PAL signal capture
LSB steganography and maze solve automation
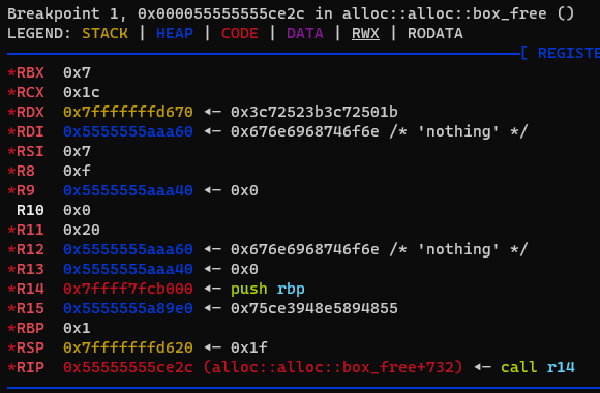
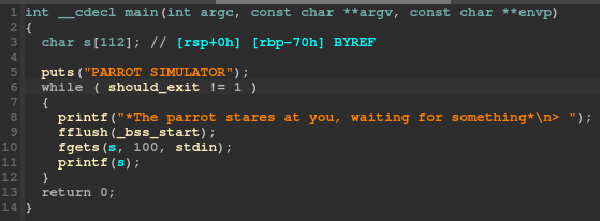
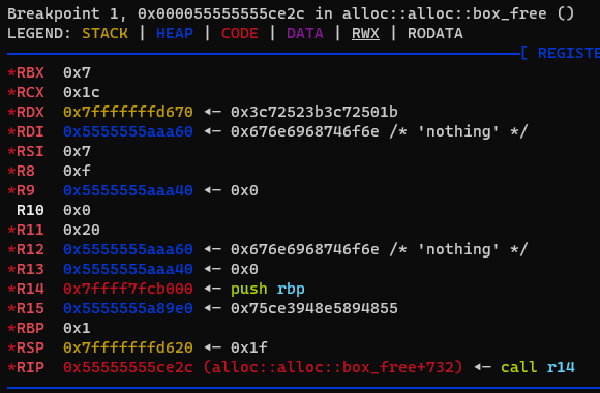
Format string exploitation to write a ROP chain on the stack
Reverse of dynamic mmaped shellcode execution
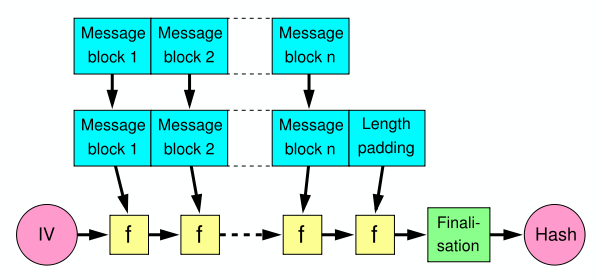
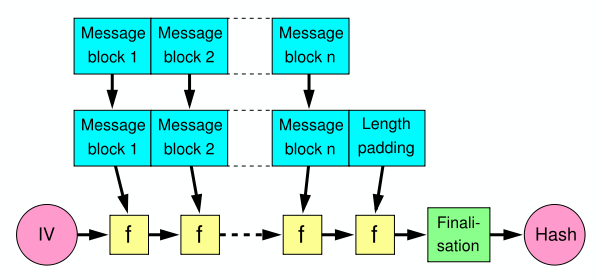
Length extension attack to forge a valid hash
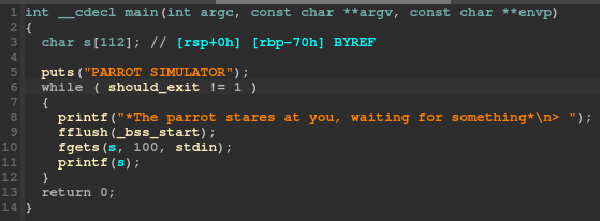
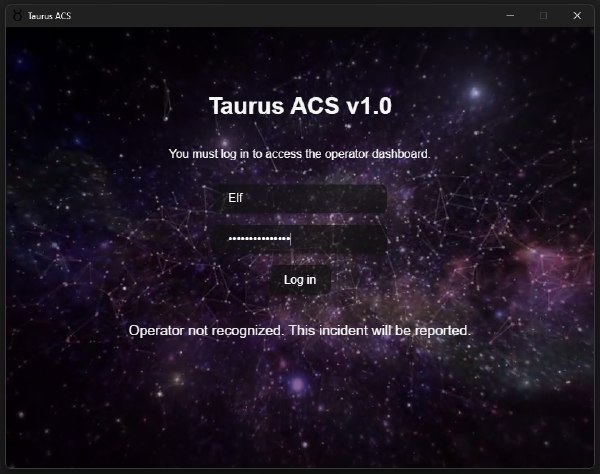
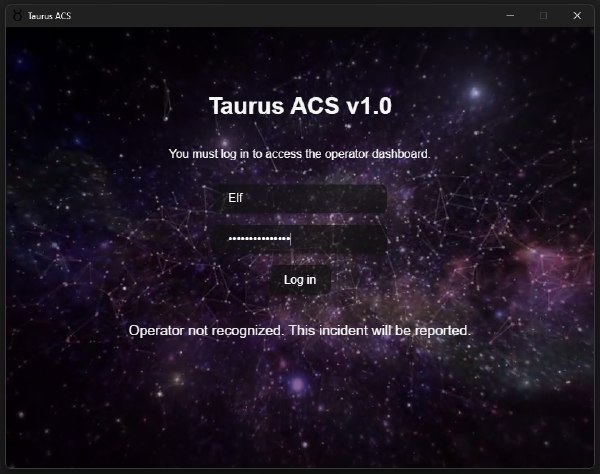
Tauri application reverse