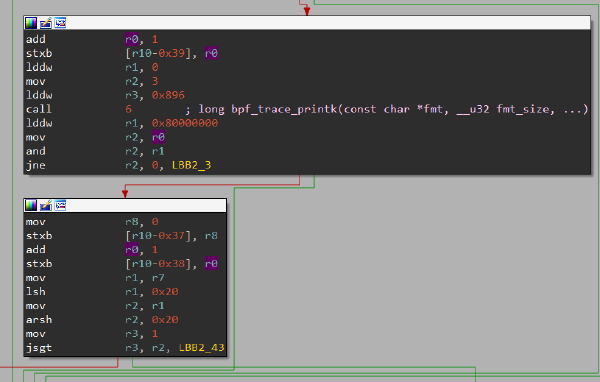
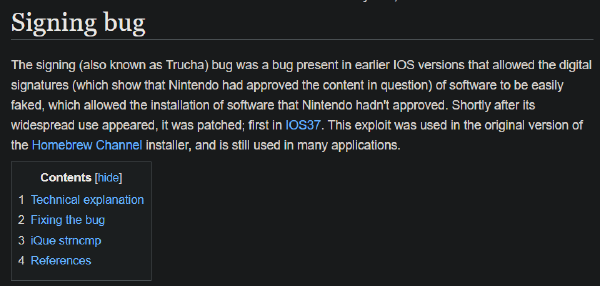
RSA signature bypass due to vulnerable implementation
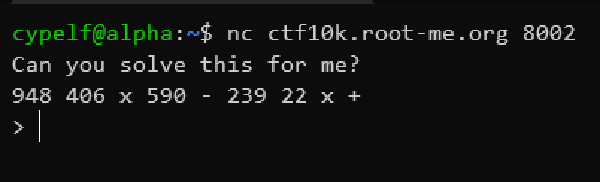
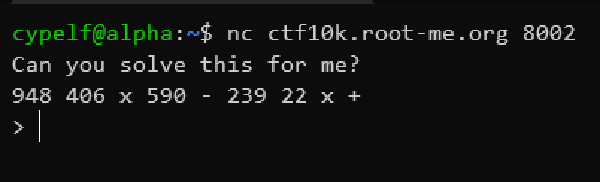
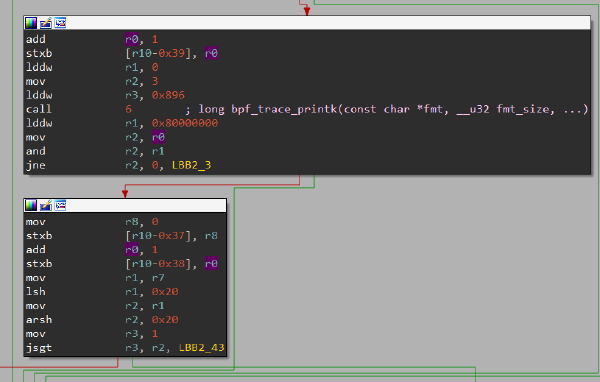
Reverse polish notation expressions computation
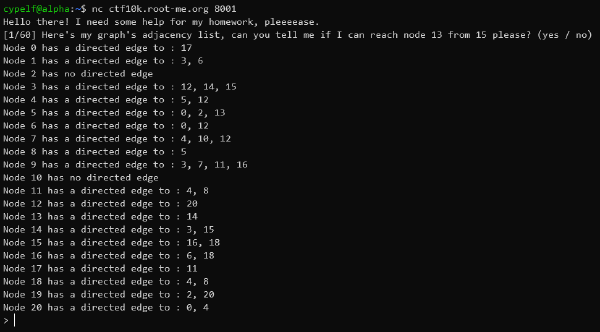
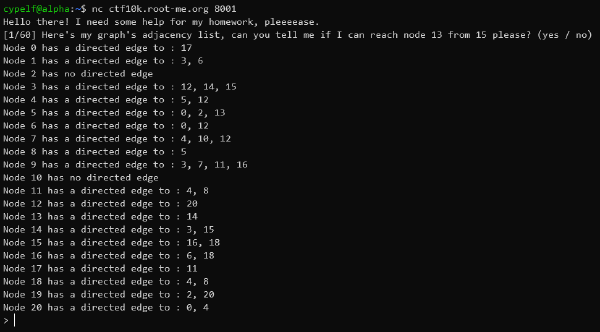
Depth first search algorithm application on an oriented graph
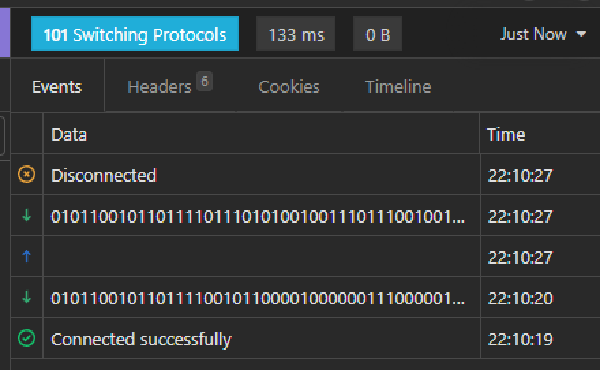
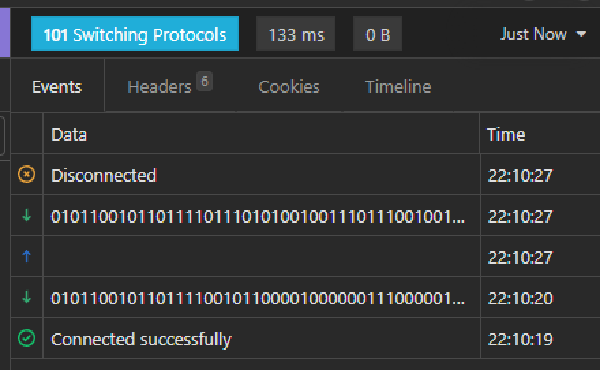
Websocket based physics quizz automation
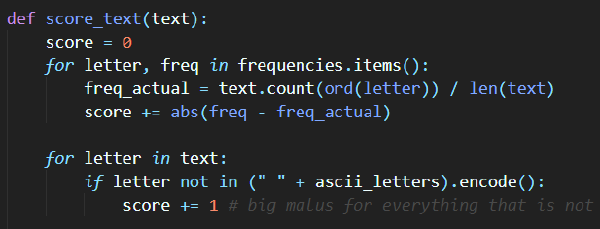
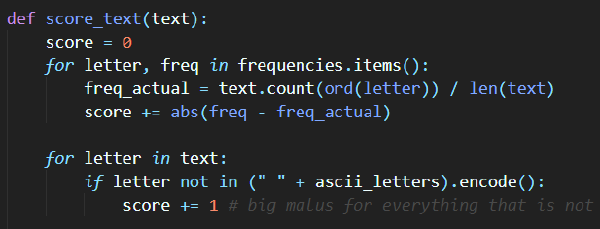
Hamming distances computation and frequency analysis to recover an unknown XOR encoded message
CQL injection and database leak into incremental ASCII hash bruteforce
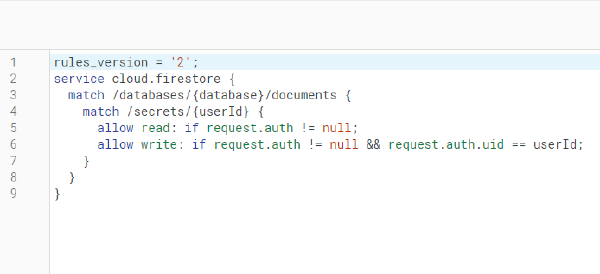
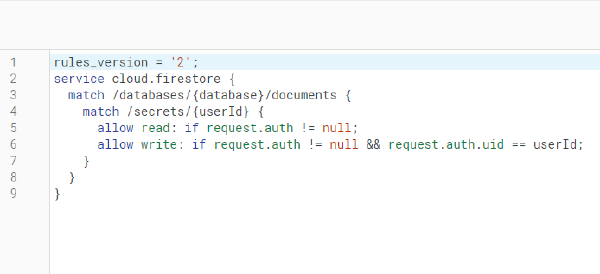
Firestore security rules misconfiguration
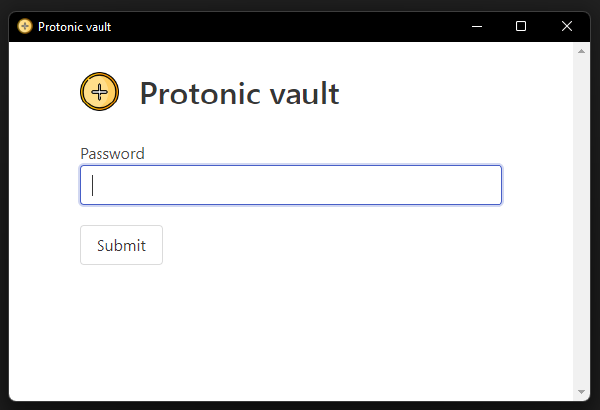
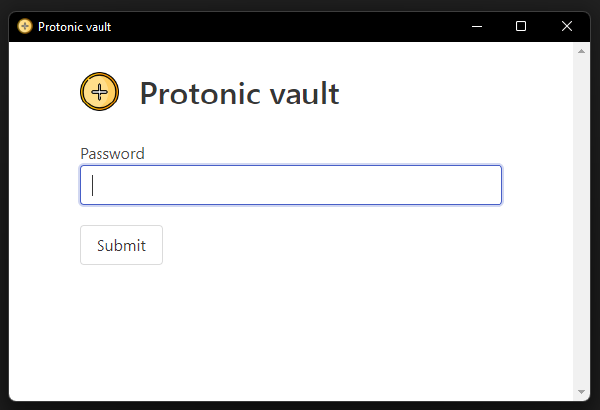
Bytenode encoded Electron application bypass